Identify The Concept Used To Determine The Derivative Classification
Arias News
Apr 06, 2025 · 6 min read
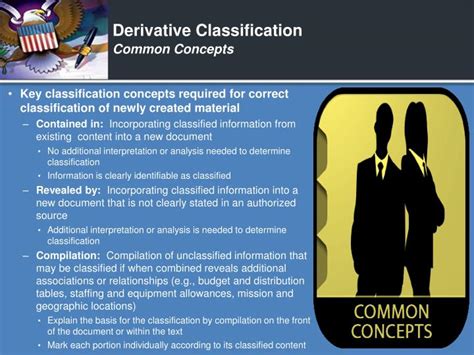
Table of Contents
Identifying the Concept Used to Determine Derivative Classification
Derivative classification is a crucial aspect of information security and management, particularly within government and military contexts. Understanding the underlying concepts that govern this process is paramount for ensuring the proper handling and protection of classified information. This article delves deep into the intricacies of derivative classification, exploring the core principles, methodologies, and potential challenges involved in determining when and how information inherits a security classification.
What is Derivative Classification?
Derivative classification is the process of assigning a security classification to information that is derived from already classified information. This isn't simply copying existing classified material; it involves a nuanced understanding of how new information relates to and inherits the security characteristics of its source. It's not about the physical act of copying, but the inherent security implications of the new information itself. The derived information may be a summary, analysis, compilation, or any other form of transformation of the original classified material. However, the key point is that the new information's classification is a direct consequence of its relationship to the already classified source.
The Core Principle: Inherent Security Implications
The foundation of derivative classification rests on the inherent security implications of the derived information. This principle dictates that the new information must be classified at a level sufficient to protect the underlying classified information it's based on. Simply put, if revealing the derived information could compromise the classified source, then the derived information must also be classified. This principle avoids the risk of indirect disclosure, where revealing seemingly innocuous information could lead to a breach of classified material.
Key Considerations in Determining Derivative Classification
Several key considerations guide the process of determining derivative classification. These factors work in conjunction to ensure that the assigned classification accurately reflects the security risks associated with the derived information.
1. Source Material Classification
The classification level of the source material is the starting point. The derived information cannot be classified higher than the highest level of classification of its source. If the source is classified "Secret," the derivative information cannot be classified "Top Secret," even if the analysis is particularly sensitive. However, the derived information might be classified at the same level as the source or even a lower level, depending on the context and its inherent sensitivity.
2. Relationship to Source Material
The nature of the relationship between the source material and the derived information is critical. A simple verbatim copy will generally inherit the same classification as the original. However, summaries, analyses, and reinterpretations might require a different classification based on the degree to which they reveal sensitive information. A nuanced understanding of how the new information relates to and builds upon the original is essential.
Example: A "Secret" intelligence report about enemy troop movements might lead to a "Confidential" summary focusing on general trends without revealing specific locations or troop counts. The summary, while derived, possesses a lower classification due to the reduced level of sensitive information it contains.
3. Context and Potential Impact
The context in which the derived information is used and its potential impact should be considered carefully. A piece of information might be considered relatively innocuous in isolation but become highly sensitive when combined with other information. The potential for damage or compromise resulting from the disclosure of the derived information is a key determinant of its classification.
Example: A seemingly harmless map of a region might be "Confidential" if it reveals the location of a secret military facility when coupled with other classified documents.
4. Specific Classification Guidance
In many cases, there will be specific guidance or instructions provided by the governing agency or organization regarding the handling of classified information and the determination of derivative classification. These guidelines often outline specific procedures, examples, and criteria to aid in the process. Adherence to these established procedures is crucial for maintaining consistency and accuracy in classification.
The Process of Derivative Classification
The process of derivative classification is typically a multi-step procedure that involves careful review and assessment by authorized personnel.
1. Identification of Source Material
The first step is accurately identifying all the source materials used in creating the derived information. This involves meticulous record-keeping and a thorough understanding of which documents or communications contributed to the creation of the new material. Any uncertainty regarding the source material must be resolved before proceeding.
2. Assessment of Security Implications
This crucial step involves a detailed analysis of the derived information to determine its inherent security implications. This assessment considers the factors discussed above: the source material's classification, the relationship to the source, the context, and any relevant specific guidance. This is frequently performed by individuals with the appropriate security clearance and expertise.
3. Classification Determination
Based on the assessment, a classification level is assigned to the derived information. This must align with established security policies and regulations. The classification must be clearly marked on the derived information using standard marking conventions.
4. Review and Approval
In most instances, the assigned classification requires review and approval by a designated authority. This ensures that the classification is accurate, consistent, and compliant with organizational policies. This step adds an extra layer of control and oversight to the process.
5. Documentation and Record Keeping
Detailed documentation is crucial. All steps in the derivative classification process must be carefully recorded, along with the rationale behind the classification assigned to the derived information. This record-keeping is essential for accountability and transparency, and provides a clear audit trail for future review.
Challenges in Derivative Classification
While the process appears straightforward, derivative classification can present significant challenges.
1. Subjectivity and Interpretation
The interpretation of security implications can sometimes be subjective. Different individuals might assess the same derived information differently, leading to inconsistencies in classification. Clear guidelines and consistent training are needed to mitigate this issue.
2. Complexity of Information Flows
In modern environments, information flows are complex, involving multiple sources and numerous transformations. Tracking the origin and security implications of all contributing factors can be challenging, potentially leading to errors in classification.
3. Evolving Threats and Technology
The nature of security threats and technologies is constantly evolving. Derivative classification procedures must adapt to account for new risks and ensure that classified information remains adequately protected.
4. Human Error
Like any human process, derivative classification is susceptible to human error. Careless mistakes in record-keeping, assessment, or documentation can lead to misclassification, compromising security.
Conclusion
Derivative classification is a complex but essential process for safeguarding sensitive information. The core principle of inherent security implications serves as the foundation, guiding the detailed assessment and careful consideration of source material, relationships, context, and potential impact. While challenges exist, consistent application of established procedures, robust training, and adherence to clearly defined guidelines are crucial to maintaining the integrity and effectiveness of the derivative classification process. Understanding these concepts is not merely a matter of compliance; it's a critical element in protecting national security and organizational interests. Ongoing education and training are vital to ensure that personnel involved in handling classified information are fully equipped to navigate the complexities of derivative classification, thereby preventing breaches and ensuring the effective protection of sensitive data.
Latest Posts
Latest Posts
-
How Many Sundays Are In One Year
Apr 06, 2025
-
Which Character Is The Best Example Of An Archetype
Apr 06, 2025
-
How Many Hours Is 2pm To 6pm
Apr 06, 2025
-
Who Is The Mother Of Yannis Daughter Krystal
Apr 06, 2025
-
What Is The Lcm Of 25 And 15
Apr 06, 2025
Related Post
Thank you for visiting our website which covers about Identify The Concept Used To Determine The Derivative Classification . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
